Inventory Security and Compliance
Protect sensitive inventory data with enterprise-grade access controls, audit trails, and compliance-ready security policies.
Role-Based Access Control
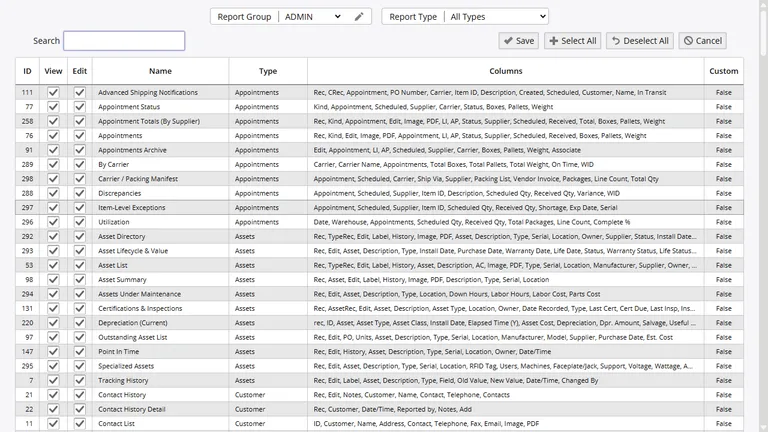
InventoryPro enforces the principle of least privilege through a layered permissions system. Security groups define which modules, reports, screens, and operations each user role can access at the individual feature level.
- Per-warehouse, per-supplier, per-customer scope restrictions
- Module, report, and data export access granularity
- Vendor and customer portal isolation
Internal staff, external partners, and auditors each see exactly what they need and nothing more. Multi-dimensional access controls ensure data isolation across organizational boundaries.
Single Sign-On Integration
For organizations managing authentication centrally, InventoryPro integrates with Single Sign-On infrastructure including Active Directory and smart card systems. Users authenticate once through their organization's identity provider and gain access to InventoryPro without a separate login. This reduces credential management overhead, eliminates password fatigue, and strengthens security by using your existing identity governance controls.
SSO integration is particularly valuable for government agencies and defense contractors that require Common Access Card (CAC) authentication. The platform accommodates these requirements without custom development, enabling federal organizations to deploy InventoryPro within their existing security architecture.
Password and Session Security
InventoryPro provides configurable password and session policies that align with organizational security standards. Administrators control minimum password length, complexity requirements, maximum password age, password history enforcement, and account lockout thresholds. Forced password resets ensure that administratively assigned temporary passwords are changed on first login.
Session management includes configurable inactivity timeouts and IP-based login attempt limits. After a defined number of failed login attempts, accounts are automatically locked and require administrative intervention to reactivate. These controls align with NIST guidance on authentication and session management for federal and enterprise environments.
Password Controls
Minimum length, complexity enforcement, maximum age, history logging, and forced reset on admin change.
Session Management
Inactivity timeout, IP-based rate limiting, automatic lockout after failed attempts, and admin lockout reset.
Workflow Approvals and Process Controls
Critical operations such as purchase orders, shipping orders, and work orders can be routed through multi-level approval chains before they take effect. Approval workflows prevent unauthorized changes, create a documented authorization trail, and ensure that significant inventory movements receive proper oversight. Learn more about approval workflows and notifications.
Compliance-Ready Audit Infrastructure
Every action in InventoryPro is recorded with the responsible user, timestamp, and full transaction detail. This audit trail provides the accountability documentation that federal procurement and compliance reviewers expect. Change tracking captures modifications to records, configurations, and permissions with before-and-after values for forensic review.
For organizations pursuing or maintaining compliance certifications, InventoryPro provides the technical controls that map directly to audit requirements: user authentication, authorization enforcement, session management, change logging, and data integrity protection. Our implementation team works with your compliance officers to configure these controls according to your specific regulatory framework.
Controlled External Access
Many organizations need to share inventory visibility with customers, suppliers, or logistics partners without exposing internal operations data. InventoryPro supports external user accounts with fine-grained access restrictions. Vendor accounts see only their own items and purchase orders. Customer accounts access only their orders, history, and relevant inventory levels. Read-only mode prevents external users from modifying data while still providing the visibility they need.
These controlled access capabilities extend to reporting as well. Report permissions ensure that external partners see only the data relevant to their relationship, and warehouse-level restrictions prevent cross-facility data leakage. This approach enables collaboration with supply chain partners while maintaining the data boundaries your organization requires.
Security Built for Regulated Environments
Our team will review your compliance requirements and demonstrate how InventoryPro security controls map to your regulatory framework.